| Exam Name: | Certified Ethical Hacker (CEH) | ||
| Exam Code: | CEH-001 Dumps | ||
| Vendor: | GAQM | Certification: | Certified Ethical Hacker CEH |
| Questions: | 878 Q&A's | Shared By: | lois |
Which of the following steganography utilities exploits the nature of white space and allows the user to conceal information in these white spaces?
What techniques would you use to evade IDS during a Port Scan? (Select 4 answers)
A Trojan horse is a destructive program that masquerades as a benign application. The software initially appears to perform a desirable function for the user prior to installation and/or execution, but in addition to the expected function steals information or harms the system.
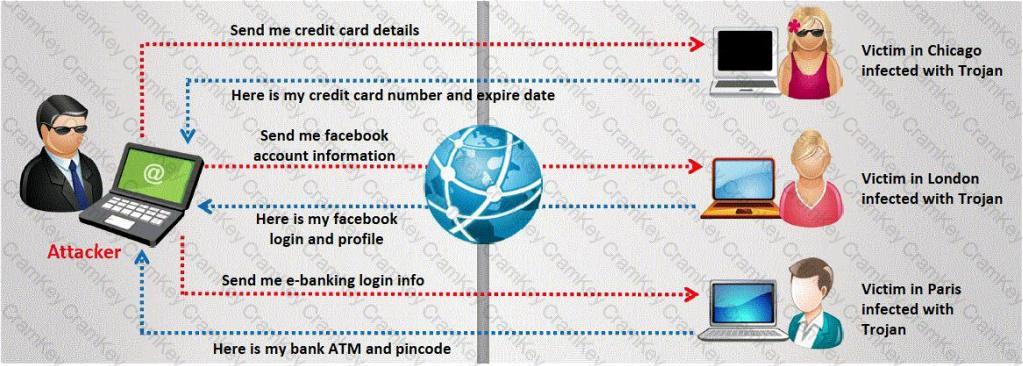
The challenge for an attacker is to send a convincing file attachment to the victim, which gets easily executed on the victim machine without raising any suspicion. Today's end users are quite knowledgeable about malwares and viruses. Instead of sending games and fun executables, Hackers today are quite successful in spreading the Trojans using Rogue security software.
What is Rogue security software?