| Exam Name: | CompTIA CySA+ Certification Exam (CS0-002) | ||
| Exam Code: | CS0-002 Dumps | ||
| Vendor: | CompTIA | Certification: | CompTIA CySA+ |
| Questions: | 372 Q&A's | Shared By: | ashley |
Which of the following is a reason to use a nsk-based cybersecunty framework?
A security analyst is investigating an active threat of the system memory. While narrowing down the source of the threat, the analyst is inspecting all processes to isolate suspicious activity Which of the following techniques is the analyst using?
A security analyst found an old version of OpenSSH running on a DMZ server and determined the following piece of code could have led to a command execution through an integer overflow;

Which of the following controls must be in place to prevent this vulnerability?
A security analyst is reviewing the following Internet usage trend report:
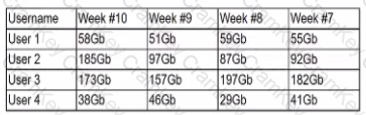
Which of the following usernames should the security analyst investigate further?