| Exam Name: | Certified Professional Ethical Hacker (CPEH) | ||
| Exam Code: | CPEH-001 Dumps | ||
| Vendor: | GAQM | Certification: | Information Systems Security |
| Questions: | 736 Q&A's | Shared By: | kira |
Craig received a report of all the computers on the network that showed all the missing patches and weak passwords. What type of software generated this report?
Which Metasploit Framework tool can help penetration tester for evading Anti-virus Systems?
Cryptography is the practice and study of techniques for secure communication in the presence of third parties (called adversaries.) More generally, it is about constructing and analyzing protocols that overcome the influence of adversaries and that are related to various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation. Modern cryptography intersects the disciplines of mathematics, computer science, and electrical engineering. Applications of cryptography include ATM cards, computer passwords, and electronic commerce.
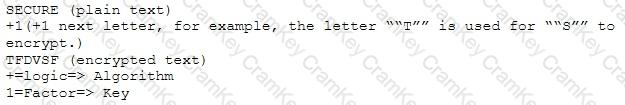
Basic example to understand how cryptography works is given below:
Which of the following choices is true about cryptography?