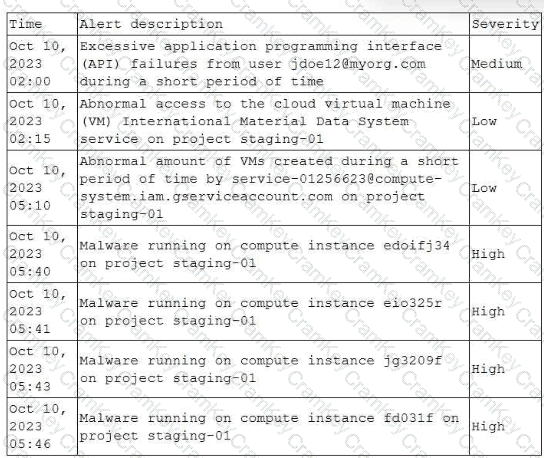
To identify the initial compromise, the analyst should start with the earliest suspicious activity in the timeline and pivot into the audit logs for the principal (identity) associated with that first alert.
Here, the first notable event is 02:00 excessive API failures tied to jdoe12@myorg.com. That commonly indicates password guessing, token misuse, or other authentication abuse attempts. The next events (02:15 metadata service access, 05:10 mass VM creation by a service account, 05:40 malware) look like follow-on activity after an initial foothold. Therefore, the best first step is to check whether those API failures were followed by any successful API calls by that user and then correlate those successful actions to the later stages in project staging-01.
This approach aligns with CySA+ guidance that analysts should use logs + timestamps to build a timeline and correlate events across identities/systems to understand scope and progression:
Sybex emphasizes correlating events from multiple sources and using that correlation to determine scope and impact:Exact extract (Sybex Study Guide): “Security analysts are often asked to help analyze that data… Knowing if other events are correlated with the initial event… [and] understanding what systems, users, services, or other assets were involved…”
Secbay underscores that logs and timestamps are key to forming an accurate incident timeline (which is exactly what we’re doing by starting from the earliest alert):Exact extract (Secbay Press): “System and application logs with timestamps help create a timeline of events, aiding in understanding when specific actions occurred during the incident.”
Why Option B is best vs. the others
B starts with the earliest suspicious identity and seeks successful API activity that would confirm compromise and explain subsequent actions (metadata access → service account actions → malware).
A is too broad initially (“all activity under project staging-01”) and anchors on a VM that only appears later; it’s not the best first pivot when you already have an earlier suspect identity.
C starts at the compute-instance phase (05:10) rather than the earliest authentication/API anomaly (02:00), so it’s more likely to find post-compromise actions rather than the initial entry.
D anchors on a specific later VM (fd031f) and compute APIs, again likely after the initial compromise.
References (CompTIA CySA+ CS0-003 documents / study guides used):
Mike Chapple & David Seidl, CompTIA CySA+ Study Guide (CS0-003): correlate other events with the initial event; identify involved users/systems/services
Secbay Press, CompTIA CySA+ Exam Prep Guide (CS0-003): logs + timestamps build a timeline of events and support analysis of incident progression