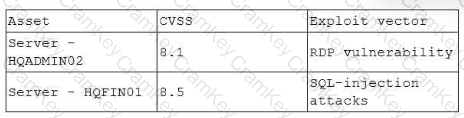
When two vulnerabilities are both high severity (CVSS 8.1 and 8.5) and no compensating controls exist, the deciding factor for remediation prioritization becomes business impact and asset criticality/value (what matters most to the organization if compromised or taken offline for remediation).
That is exactly what a Business Impact Analysis (BIA) is used for: it is a formalized method to determine asset criticality/value designations and to prioritize response/remediation work based on business impact.
Supporting exact extracts:
The Secbay Press CS0-003 guide explicitly states that Business Impact Analysis is used to align vulnerability prioritization with critical business functions:Exact extract (Secbay Press): “Business Impact Analysis: … Considers the potential impact of vulnerabilities on critical business functions … prioritizing vulnerabilities that could impact core business processes.”
It also describes the vulnerability prioritization process as combining severity/exploitability with asset criticality assessment (which is informed by business owners and BIA outputs):Exact extract (Secbay Press): “Asset Criticality Assessment: Evaluate the criticality of assets affected… Consider the importance of assets in business operations, data sensitivity, and regulatory compliance.”
The All-in-One CS0-003 guide reinforces that asset value (sensitivity + criticality) is one of the most important drivers of remediation timing/prioritization:Exact extract (All-in-One Exam Guide): “Asset value is… one of the most important factors in determining how quickly you should remediate vulnerabilities…” and asset value is tied to “sensitivity and criticality.”
Applying this to the scenario
HQFIN01 supports financial transactions for the largest business unit → typically extremely high criticality (availability) and often high sensitivity/integrity requirements.
HQADMIN02 is used by a privileged user and could be high risk too (admin access), but the question asks what the team would do to determine prioritization: the correct step is to reference BIA/value designation and then prioritize based on which asset is more critical to business operations.
Why the other options are incorrect
A (Review BCP and patch what takes longer to bring online): BCP/DR planning is not the primary method for vulnerability remediation ranking; prioritization is risk-based and commonly driven by asset criticality/business impact (BIA), not “time to bring online.”
B (Fix the faster one first): Speed of remediation is not the main driver; risk reduction and business impact are.
D (Least recent backups): Backup recency matters for recovery and resilience, but it’s not the primary determinant for vulnerability remediation priority versus asset criticality and business impact.
References (CompTIA CySA+ CS0-003 documents / study guides used):
Secbay Press, CompTIA CySA+ Exam Prep Guide (CS0-003): BIA used to prioritize vulnerabilities impacting critical business functions; asset criticality assessment in prioritization process
Mya Heath et al., CompTIA CySA+ All-in-One Exam Guide (CS0-003): asset value (sensitivity + criticality) drives how quickly vulnerabilities should be remediated