| Exam Name: | PECB Certified ISO/IEC 27001 2022 Lead Auditor exam | ||
| Exam Code: | ISO-IEC-27001-Lead-Auditor Dumps | ||
| Vendor: | PECB | Certification: | ISO 27001 |
| Questions: | 418 Q&A's | Shared By: | shanaya |
You are an ISMS auditor conducting a third-party surveillance audit of a telecom's provider. You are in the equipment staging room where network switches are pre-programmed before being despatched to clients. You note that recently there has been a significant increase in the number of switches failing their initial configuration test and being returned for reprogramming.
You ask the Chief Tester why and she says, 'It's a result of the recent ISMS upgrade'. Before the upgrade each technician had their own hard copy work instructions. Now, the eight members of my team have to share two laptops to access the clients' configuration instructions online. These delays put pressure on the technicians, resulting in more mistakes being made'.
Based solely on the information above, which clause of ISO to raise a nonconformity against' Select one.
Which two of the following phrases would apply to "plan" in relation to the Plan-Do-Check-Act cycle for a business process?
Retaining documentation
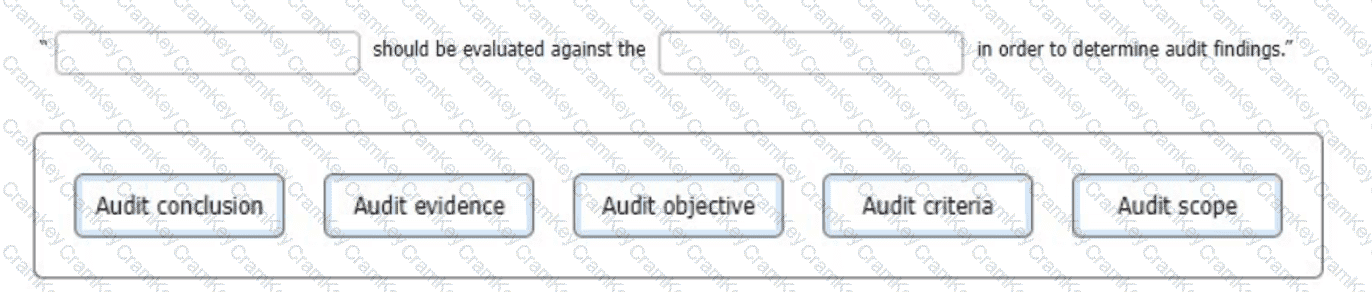
In regard to generating an audit finding, select the words that best complete the following sentence.
To complete the sentence with the best word(s), click on the blank section you want to complete so that it Is highlighted in red, and then click on the applicable text from the options below. Alternatively, you may drag and drop the option to the appropriate blank section.