| Exam Name: | Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) | ||
| Exam Code: | 200-201 Dumps | ||
| Vendor: | Cisco | Certification: | CyberOps Associate |
| Questions: | 476 Q&A's | Shared By: | bryan |
Refer to the exhibit.
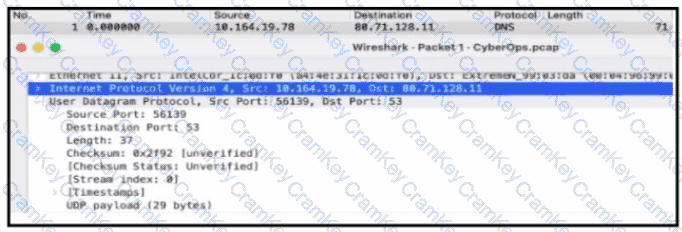
What kind of activity occurs in the network?
An analyst discovers that a legitimate security alert has been dismissed. Which signature caused this impact on network traffic?