| Exam Name: | Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) | ||
| Exam Code: | 300-215 Dumps | ||
| Vendor: | Cisco | Certification: | CyberOps Professional |
| Questions: | 131 Q&A's | Shared By: | lois |
A cybersecurity analyst must identify an unknown service causing high CPU on a Windows server. What tool should be used?
Refer to the exhibit.
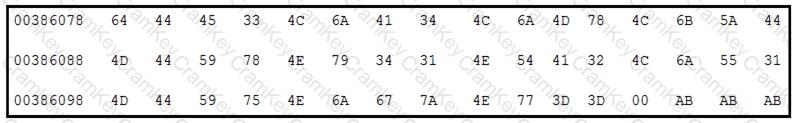
Which encoding technique is represented by this HEX string?
A cybersecurity analyst detects fileless malware activity on secure endpoints. What should be done next?
A threat actor attempts to avoid detection by turning data into a code that shifts numbers to the right four times. Which anti-forensics technique is being used?