CompTIA SecurityX Certification Exam
Last Update Jun 11, 2026
Total Questions : 344
To help you prepare for the CAS-005 CompTIA exam, we are offering free CAS-005 CompTIA exam questions. All you need to do is sign up, provide your details, and prepare with the free CAS-005 practice questions. Once you have done that, you will have access to the entire pool of CompTIA SecurityX Certification Exam CAS-005 test questions which will help you better prepare for the exam. Additionally, you can also find a range of CompTIA SecurityX Certification Exam resources online to help you better understand the topics covered on the exam, such as CompTIA SecurityX Certification Exam CAS-005 video tutorials, blogs, study guides, and more. Additionally, you can also practice with realistic CompTIA CAS-005 exam simulations and get feedback on your progress. Finally, you can also share your progress with friends and family and get encouragement and support from them.
A systems engineer is configuring SSO for a business that will be using SaaS applications for its remote-only workforce. Privileged actions in SaaS applications must be allowed only from corporate mobile devices that meet minimum security requirements, but BYOD must also be permitted for other activity. Which of the following would best meet this objective?
An organization with a remote workforce has a new client with the following requirements:
Consultants need to travel to the client site.
The company has proprietary information on its hard drives.
The company prohibits BYOD.
Which of the following would be the most beneficial for the organization to implement?
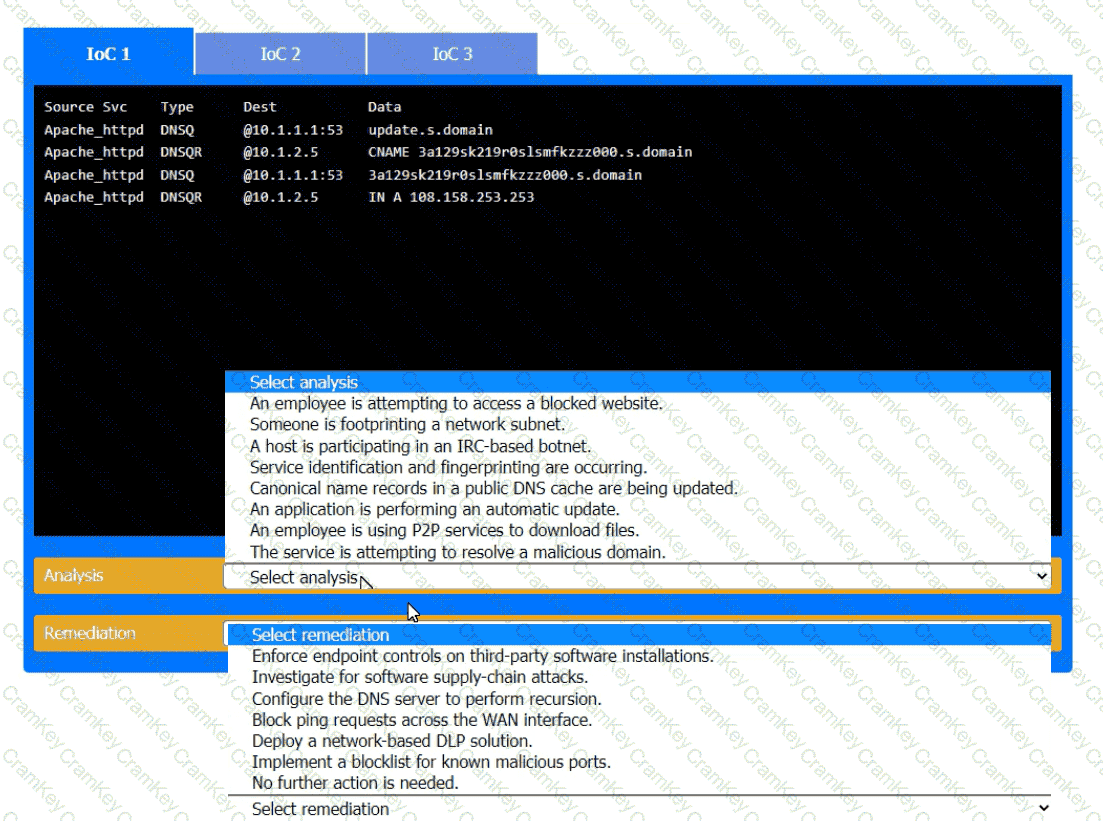
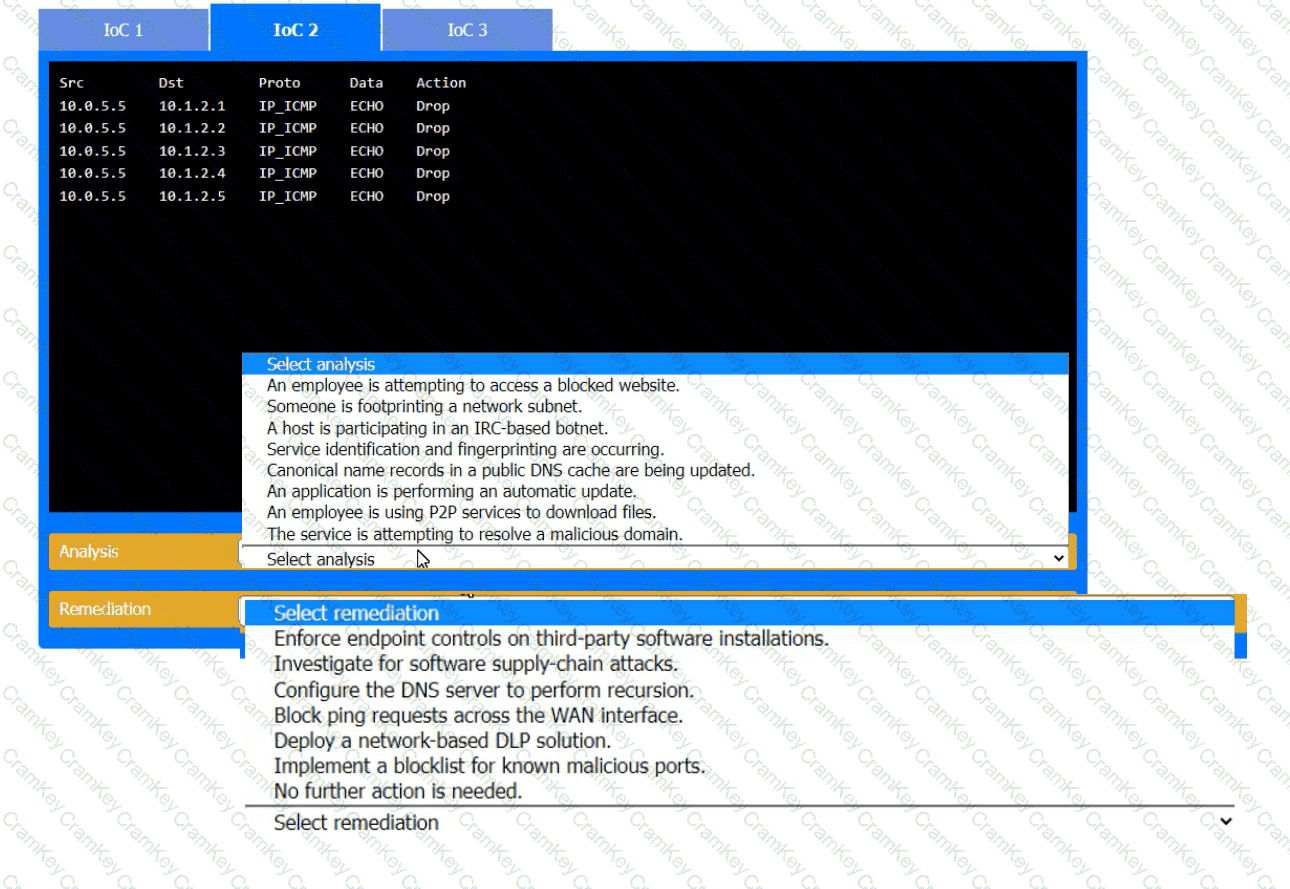
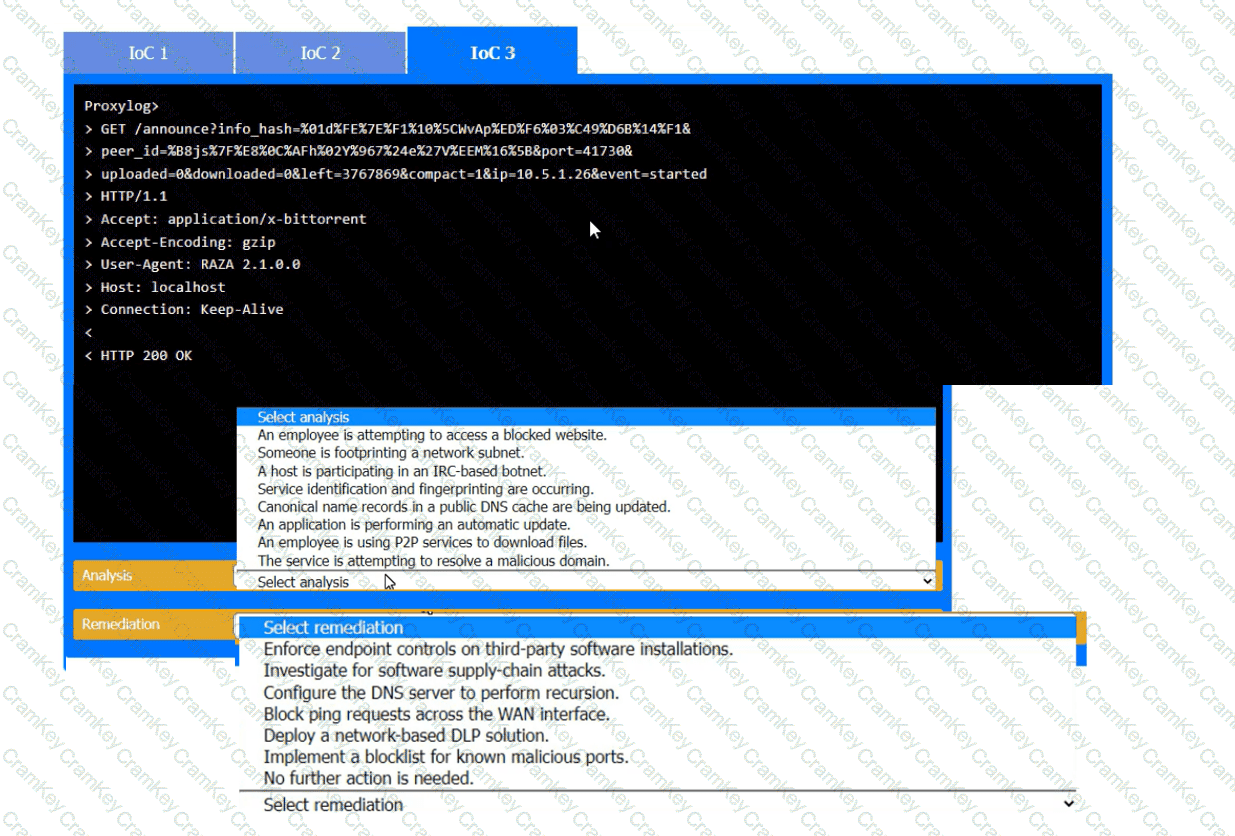
During the course of normal SOC operations, three anomalous events occurred and were flagged as potential IoCs. Evidence for each of these potential IoCs is provided.
INSTRUCTIONS
Review each of the events and select the appropriate analysis and remediation options for each IoC.
As part of a security audit in the software development life cycle, a product manager must demonstrate and provide evidence of a complete representation of the code and modules used within the production-deployed application prior to the build. Which of the following best provides the required evidence?