EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing
Last Update Jun 10, 2026
Total Questions : 201
To help you prepare for the ECSAv10 ECCouncil exam, we are offering free ECSAv10 ECCouncil exam questions. All you need to do is sign up, provide your details, and prepare with the free ECSAv10 practice questions. Once you have done that, you will have access to the entire pool of EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing ECSAv10 test questions which will help you better prepare for the exam. Additionally, you can also find a range of EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing resources online to help you better understand the topics covered on the exam, such as EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing ECSAv10 video tutorials, blogs, study guides, and more. Additionally, you can also practice with realistic ECCouncil ECSAv10 exam simulations and get feedback on your progress. Finally, you can also share your progress with friends and family and get encouragement and support from them.
Which of the following is NOT related to the Internal Security Assessment penetration testing strategy?
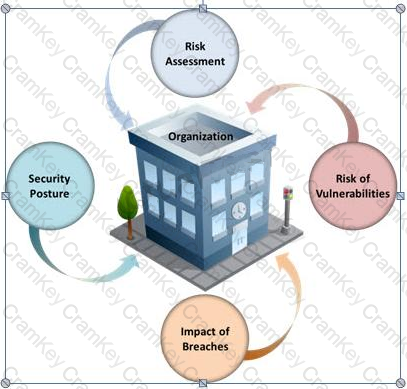
Many security and compliance projects begin with a simple idea: assess the organization's risk, vulnerabilities, and breaches. Implementing an IT security risk assessment is critical to the overall security posture of any organization.
An effective security risk assessment can prevent breaches and reduce the impact of realized breaches.
What is the formula to calculate risk?
Which of the following equipment could a pen tester use to perform shoulder surfing?
Which of the following statements is true about Multi-Layer Intrusion Detection Systems (mIDSs)?