| Exam Name: | Designing Cisco Security Infrastructure (300-745 SDSI) v1.0 | ||
| Exam Code: | 300-745 Dumps | ||
| Vendor: | Cisco | Certification: | CCNP Security |
| Questions: | 58 Q&A's | Shared By: | melania |
Refer to the exhibit.
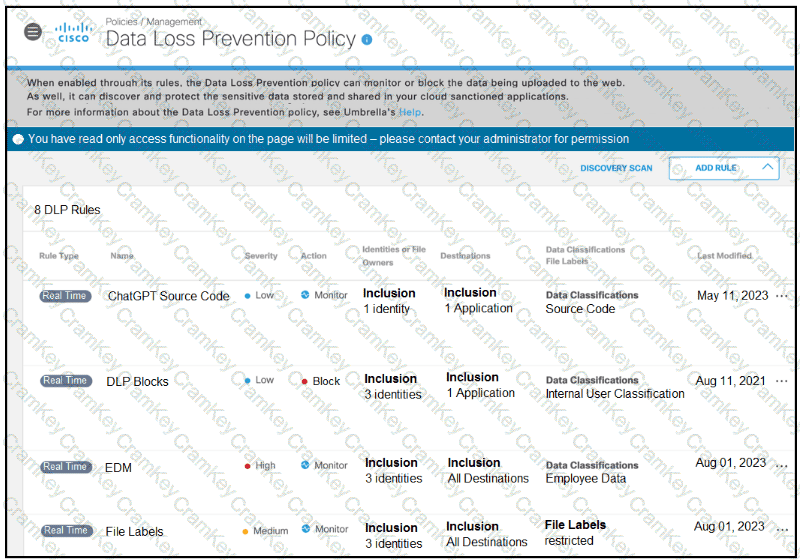
A software developer noticed that the application source code had been found on the internet. To avoid such an incident from happening again, the developer applied a DLP policy to prevent from uploading source code into generative AI tool like ChatGPT. When testing the policy, the developer noticed that it is still possible for the source code to be uploaded. Which action must the developer take to prevent this issue?
A company has been facing recurring issues with SQL injection vulnerabilities affecting the products, leading to significant disruptions for customers. To address the security concerns proactively, the company wants to integrate a tool into the CI/CD pipeline. The tool must be capable of identifying vulnerabilities such as SQL injection early in the development process, which allows developers to rectify issues before the code is deployed. Which solution must be implemented to meet the requirement?
A security engineer on an application design team must choose a framework of attack patterns to evaluate during threat modeling. Which framework provides the common set of attacks?
A company recently discovered that a former employee, who left to join a competitor, continued to access and exfiltrate sensitive data over several weeks after leaving. The breach highlighted vulnerabilities in the organization’s data security and access management practices. To prevent such incidents in the future, the organization must adopt measures that detect and restrict unauthorized data access and transfer. Which mitigation strategy must be implemented to address the issue?