Palo Alto Networks Network Security Analyst
Last Update Jun 2, 2026
Total Questions : 74
To help you prepare for the NetSec-Analyst Paloalto Networks exam, we are offering free NetSec-Analyst Paloalto Networks exam questions. All you need to do is sign up, provide your details, and prepare with the free NetSec-Analyst practice questions. Once you have done that, you will have access to the entire pool of Palo Alto Networks Network Security Analyst NetSec-Analyst test questions which will help you better prepare for the exam. Additionally, you can also find a range of Palo Alto Networks Network Security Analyst resources online to help you better understand the topics covered on the exam, such as Palo Alto Networks Network Security Analyst NetSec-Analyst video tutorials, blogs, study guides, and more. Additionally, you can also practice with realistic Paloalto Networks NetSec-Analyst exam simulations and get feedback on your progress. Finally, you can also share your progress with friends and family and get encouragement and support from them.
A firewall administrator implementing Palo Alto Networks best practices on the company firewall reviews NGFW alerts in Strata Cloud Manager (SCM) and determines that one alert does not apply to this environment. If the administrator has no intention to resolve the underlying issue, what is the appropriate next step?
An analyst is investigating why an App-ID for a custom application is showing as "unknown-tcp" in the Traffic logs. The application is running on port 8080. What is the most likely cause of this identification failure?
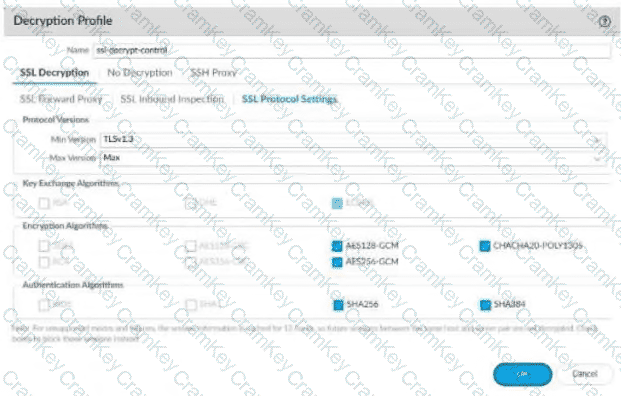
Based on the image below, what is a risk associated with this configuration?
An analyst determines that several sanctioned, predefined applications are being intermittently blocked, even though there is an existing policy permitting them. An investigation reveals that the applications are using non-standard ports, which is causing them to be blocked. The applications are critical for business operations, and the analyst has approval to allow them.
Which configuration adjustment should be implemented to ensure secure access to the applications?