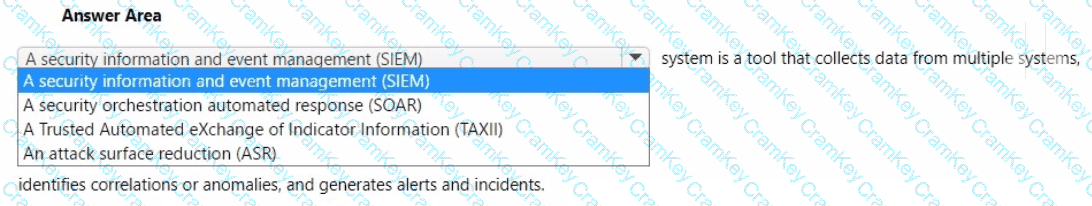
A Security Information and Event Management (SIEM) system is designed to collect and aggregate security data from multiple sources—such as servers, devices, applications, and security appliances—across an organization. It then analyzes the data for anomalies, correlations, and patterns that could indicate potential threats or breaches.
From the SCI certification learning paths, especially SC-200 (Microsoft Security Operations Analyst), Microsoft defines SIEM as follows:
“SIEM tools collect and analyze activity from multiple resources across your IT infrastructure. Microsoft Sentinel is Microsoft’s cloud-native SIEM that provides intelligent security analytics and threat intelligence to help detect and respond to security threats.”
A SIEM system:
Ingests large volumes of data (logs, events).
Uses built-in rules, AI, and analytics to identify threats.
Correlates alerts from various sources to form incidents.
Generates alerts and dashboards for security analysts.
Microsoft Sentinel, as Microsoft’s SIEM solution, embodies all of these capabilities.
Other options in the dropdown (incorrect for this context):
SOAR is focused on automating responses after SIEM alerts.
TAXII is a threat intel transport protocol, not a detection system.
ASR (Attack Surface Reduction) refers to endpoint hardening, not centralized event analysis.
✅ Therefore, the correct and Microsoft-verified term is: A security information and event management (SIEM).