Fortinet NSE 7 - Security Operations 7.6 Architect
Last Update Jun 1, 2026
Total Questions : 57
To help you prepare for the NSE7_SOC_AR-7.6 Fortinet exam, we are offering free NSE7_SOC_AR-7.6 Fortinet exam questions. All you need to do is sign up, provide your details, and prepare with the free NSE7_SOC_AR-7.6 practice questions. Once you have done that, you will have access to the entire pool of Fortinet NSE 7 - Security Operations 7.6 Architect NSE7_SOC_AR-7.6 test questions which will help you better prepare for the exam. Additionally, you can also find a range of Fortinet NSE 7 - Security Operations 7.6 Architect resources online to help you better understand the topics covered on the exam, such as Fortinet NSE 7 - Security Operations 7.6 Architect NSE7_SOC_AR-7.6 video tutorials, blogs, study guides, and more. Additionally, you can also practice with realistic Fortinet NSE7_SOC_AR-7.6 exam simulations and get feedback on your progress. Finally, you can also share your progress with friends and family and get encouragement and support from them.
Refer to the exhibits.
The FortiMail Sender Blocklist playbook is configured to take manual input and add those entries to the FortiMail abc. com domain-level block list. The playbook is configured to use a FortiMail connector and the ADD_SENDER_TO_BLOCKLIST action.
Why is the FortiMail Sender Blocklist playbook execution failing7
Refer to the exhibit.
Assume that all devices in the FortiAnalyzer Fabric are shown in the image.
Which two statements about the FortiAnalyzer Fabric deployment are true? (Choose two.)
Which statement best describes the MITRE ATT&CK framework?
Refer to the exhibit.
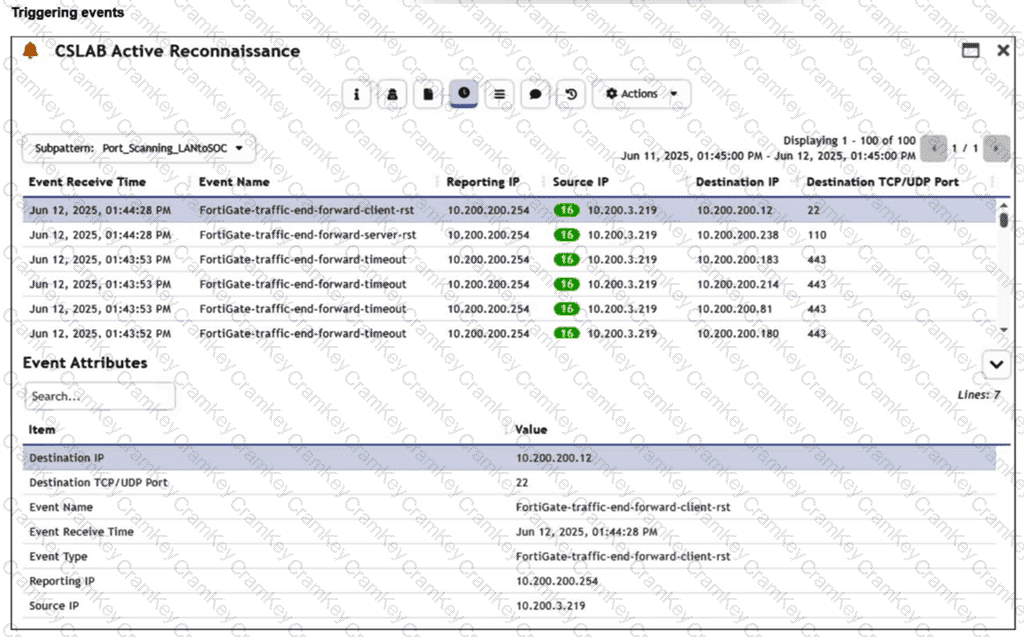
You are reviewing the Triggering Events page for a FortiSIEM incident. You want to remove the Reporting IP column because you have only one firewall in the topology. How do you accomplish this? (Choose one answer)