| Exam Name: | CompTIA PenTest+ Exam | ||
| Exam Code: | PT0-003 Dumps | ||
| Vendor: | CompTIA | Certification: | PenTest+ |
| Questions: | 330 Q&A's | Shared By: | tony |
A penetration tester is testing a power plant ' s network and needs to avoid disruption to the grid. Which of the following methods is most appropriate to identify vulnerabilities in the network?
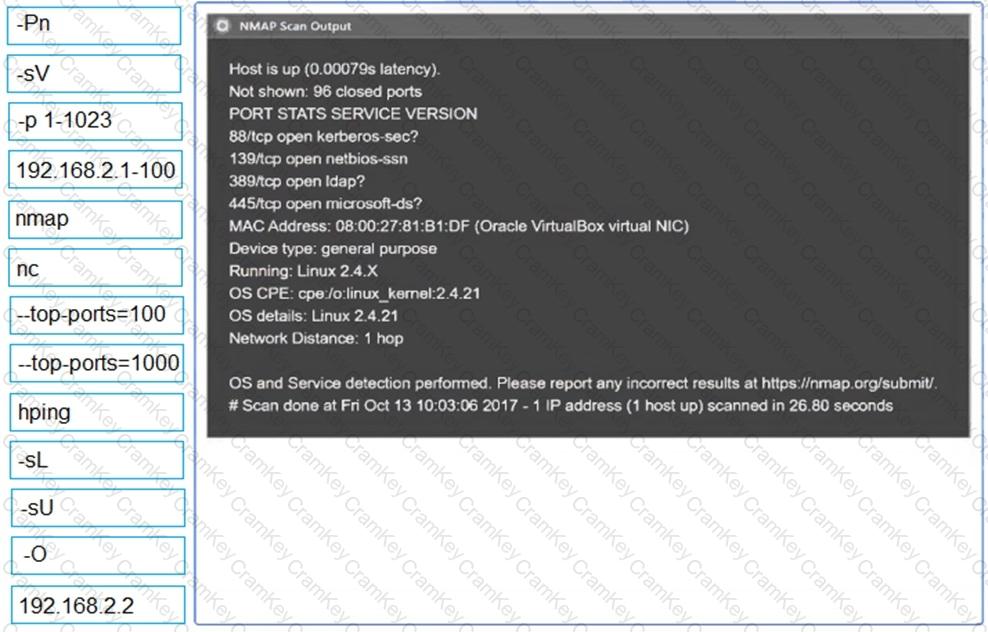
A penetration tester needs to scan a remote infrastructure with Nmap. The tester issues the following command:
nmap 10.10.1.0/24
Which of the following is the number of TCP ports that will be scanned?
A penetration tester obtains password dumps associated with the target and identifies strict lockout policies. The tester does not want to lock out accounts when attempting access. Which of the following techniques should the tester use?
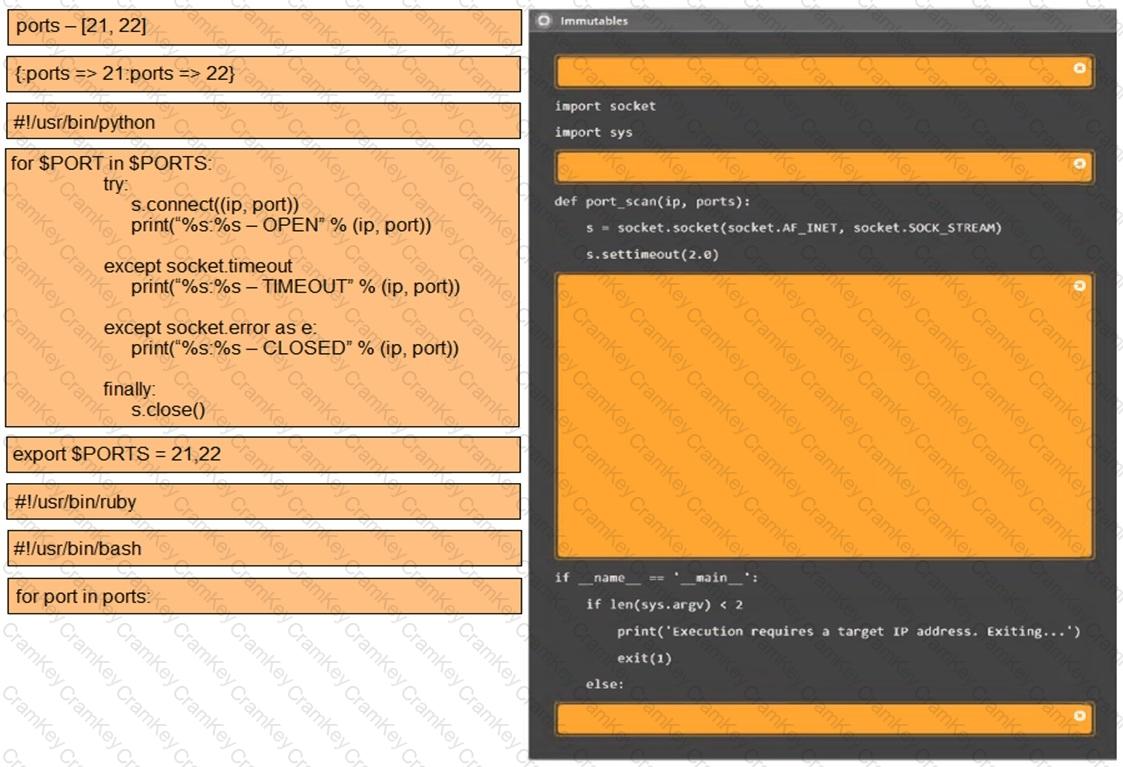
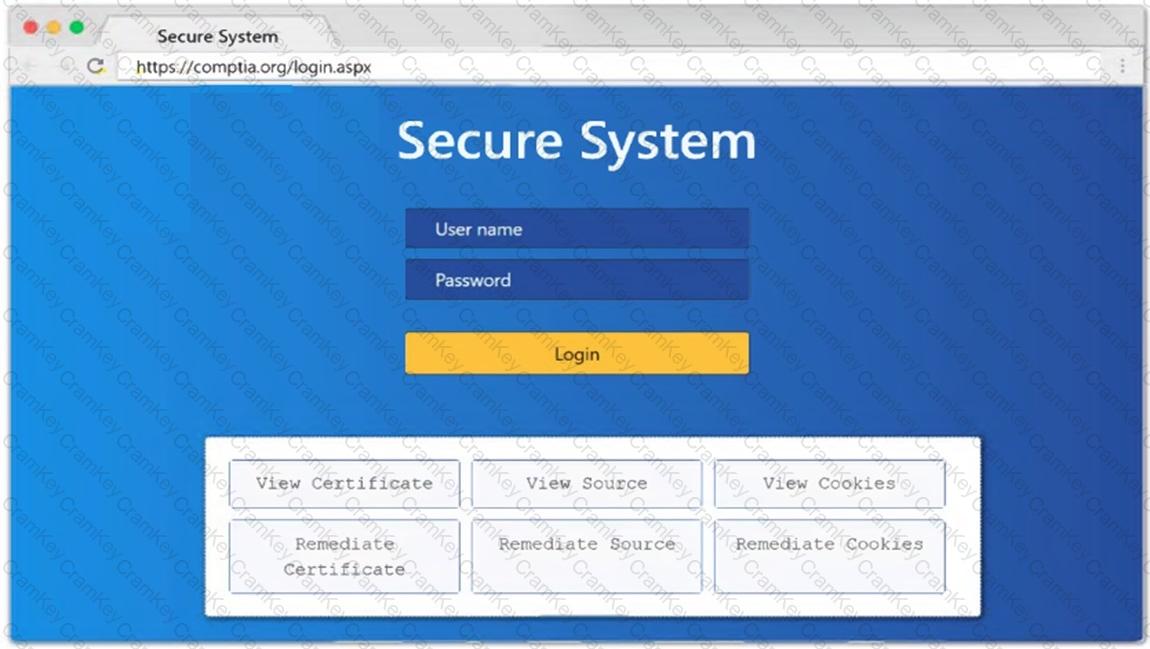
SIMULATION
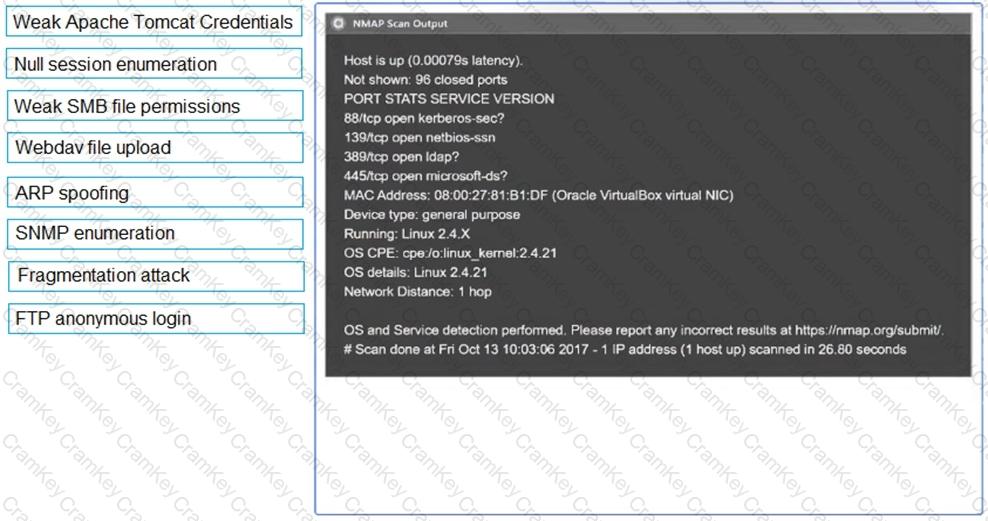
Using the output, identify potential attack vectors that should be further investigated.