| Exam Name: | Certified in Planning and Inventory Management (CPIM 8.0) | ||
| Exam Code: | CPIM-8.0 Dumps | ||
| Vendor: | APICS | Certification: | CPIM |
| Questions: | 606 Q&A's | Shared By: | alfie-james |
Which of the following sampling techniques is BEST suited for comprehensive risk assessments?
Which of the following should Business Impact Analysis (BIA) reports always include?
During a manual source code review, an organization discovered a dependency with an open-source library that has a history of being exploited. Which action should the organization take FIRST to assess the risk of depending on the open-source library?
Exhibit:
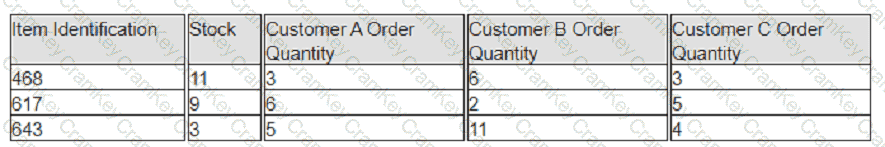
A company has prioritized customers A, B, and C, filling orders in that sequence. What are the impacts to customer service levels for customers B and C?