Dell Security Foundations Achievement
Last Update May 7, 2026
Total Questions : 20
To help you prepare for the D-SF-A-24 EMC exam, we are offering free D-SF-A-24 EMC exam questions. All you need to do is sign up, provide your details, and prepare with the free D-SF-A-24 practice questions. Once you have done that, you will have access to the entire pool of Dell Security Foundations Achievement D-SF-A-24 test questions which will help you better prepare for the exam. Additionally, you can also find a range of Dell Security Foundations Achievement resources online to help you better understand the topics covered on the exam, such as Dell Security Foundations Achievement D-SF-A-24 video tutorials, blogs, study guides, and more. Additionally, you can also practice with realistic EMC D-SF-A-24 exam simulations and get feedback on your progress. Finally, you can also share your progress with friends and family and get encouragement and support from them.
Dell Services team cannot eliminate all risks, but they can continually evaluate the resilience and preparedness ofA .R.T.I.E.by using the National Institute of Standards and Technology Cybersecurity Framework (NIST CSF).
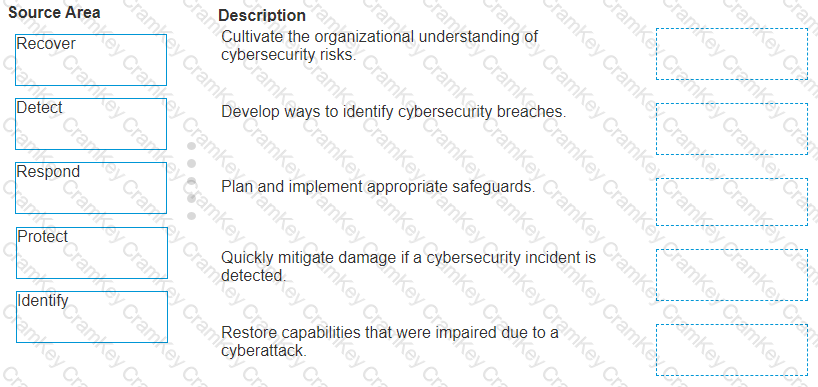
Match the core NIST CSF component functions with the description that the Dell Services team would have recommended toA .R.T.I.E.
In the cloud, there are numerous configuration options for the services provided. If not properly set, these configurations can leave the environment in an unsecure state where an attacker can read and modify the transmitted data packets and send their own requests to the client.
Which types of attack enable an attacker to read and modify the transmitted data packets and send their own requests to the client?
During the analysis, the threat intelligence team disclosed that attackers not only encrypted files, but also attempted to encrypt backups and shared, networked, and cloud drives.
Which type of ransomware is used for this attack?
To optimize network performance and reliability, low latency network path for customer traffic, A.R.T.I.E created a modern edge solution. The edge solution helped the organization to analyze and process diverse data and identify related business opportunities. Edge computing also helped them to create and distribute content and determine how the users consume it. But as compute and data creation becomes more decentralized and distributed,A .R.T.I.E.was exposed to various risks and security challenges inevitably became more complex. Unlike the cloud in a data center, it is physically impossible to wall off the edge.
Which type of edge security riskA .R.T.I.E.is primarily exposed?